Description:
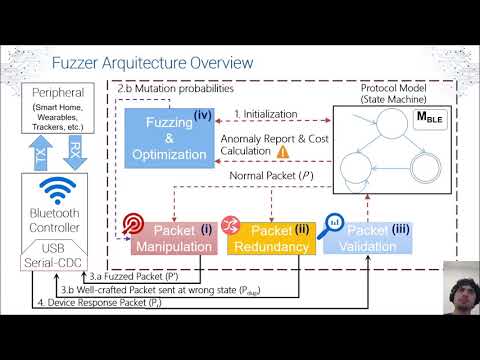
Explore the vulnerabilities in Bluetooth Low Energy (BLE) protocol implementations through this 25-minute conference talk from USENIX ATC '20. Dive into the SweynTooth framework, a systematic and comprehensive testing approach developed to fuzz BLE protocol implementations effectively. Learn about the state machine model incorporated in the framework, the fuzzing process, and how it exposes anomalies in BLE devices. Discover the impact of this research, which led to the discovery of 11 new vulnerabilities and 13 new CVE IDs across 12 devices from eight vendors and four IoT products. Gain insights into BLE security testing, fuzzing techniques, and the importance of protocol compliance in IoT devices.
SweynTooth - Unleashing Mayhem over Bluetooth Low Energy
Add to list
#Conference Talks
#USENIX Annual Technical Conference
#Information Security (InfoSec)
#Cybersecurity
#IoT security
#Vulnerability Testing
#Programming
#Software Development
#Software Testing
#Fuzzing
#Computer Science
#Computer Networking
#Bluetooth
#Bluetooth Low Energy