Description:
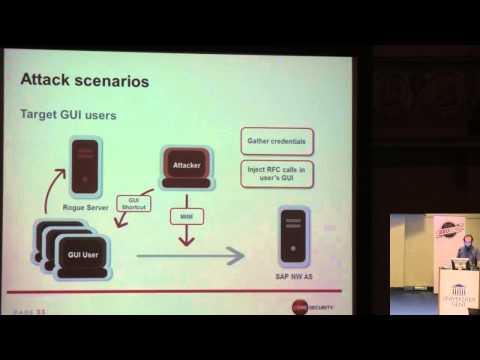
Explore the intricacies of SAP vulnerabilities in this 46-minute conference talk from BruCON Security Conference. Delve into the Diag protocol, a critical component of SAP Netweaver's application-level communications between SAP GUI and SAP Netweaver Application Servers. Discover novel approaches to uncovering vulnerabilities in SAP software through protocol analysis and manipulation tools. Learn about man-in-the-middle attacks, RFC calls injection, rogue SAP server deployment, and SAP GUI client-side attacks. Gain insights into hardening SAP installations and mitigating potential threats. Follow along as the speaker dissects the Diag protocol, highlights security concerns, and demonstrates packet dissection using the SAP plugin for Wireshark and packet crafting with pysap. Understand the fuzzing approach, explore discovered vulnerabilities, and examine various attack scenarios. Conclude with a discussion on recent changes, defense strategies, and future work in SAP security.
Uncovering SAP Vulnerabilities - Dissecting and Breaking the Diag Protocol
Add to list
#Conference Talks
#BruCON
#Information Security (InfoSec)
#Cybersecurity
#Computer Science
#Computer Networking
#Wireshark
#Penetration Testing
#Network Security
#Man in The Middle Attacks
#Business
#Sales
#Customer Relationship Management
#SAP
#SAP Security