Description:
Explore a comprehensive analysis of double-fetch bugs in operating system kernels through this IEEE conference talk. Delve into the challenges of detecting these critical vulnerabilities and learn about Deadline, a static analysis system designed to automatically identify double-fetch bugs. Discover the formal definition of these bugs, understand the limitations of previous detection methods, and gain insights into the systematic approach used to find multi-reads in kernel code. Examine the specialized symbolic checking techniques employed to verify potential double-fetch bugs and review the findings from applying Deadline to Linux and FreeBSD kernels. Investigate four generic strategies proposed for patching and preventing these vulnerabilities, based on extensive research and discussions with kernel maintainers. Gain valuable knowledge about address-based separation protection, dependency analysis, and mitigation techniques to enhance operating system security.
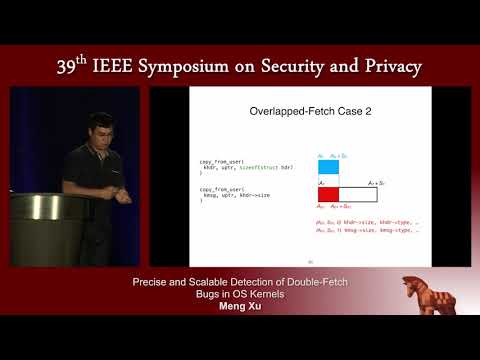
Precise and Scalable Detection of Double-Fetch Bugs in OS Kernels
Add to list
#Programming
#Software Development
#Software Testing
#Static Analysis
#Information Security (InfoSec)
#Cybersecurity
#Computer Security
#Operating System Security