Description:
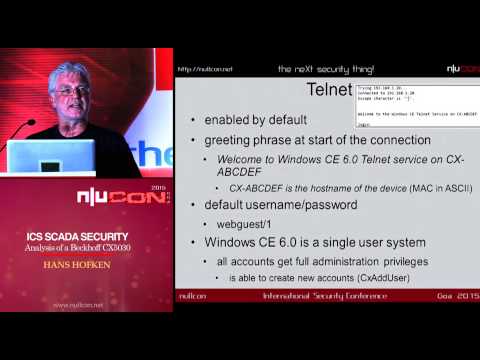
Explore a conference talk on ICS SCADA security analysis of the Beckhoff CX5020 PLC, presented at nullcon Goa 2015. Delve into the vulnerabilities of this modern PLC, which runs on a customized Windows CE 6.0 and uses Industrial Ethernet (EtherCat) for communication. Discover how rights to control the PLC program and operating system can be obtained without extensive penetration testing knowledge. Examine the challenges of securing ICS systems as standard platforms and TCP/IP-encapsulated SCADA protocols introduce hidden features and potential risks. Learn about the design and structure of SCADA systems, TwinCAT devices, and system control on the CX5020. Investigate security analysis results, including vulnerabilities in Telnet, webserver virtual directory, and SCADA services. Understand the ADS search process for devices, creation of ADS routes, and complete message flow. Explore possible attacks, including those on mschapv2, and gain insights into advisory recommendations for suppliers in the industrial control systems sector.
Read more
ICS SCADA Security Analysis of a Beckhoff CX5020 PLC
Add to list
#Conference Talks
#nullcon
#Information Security (InfoSec)
#Cybersecurity
#Computer Science
#Operating Systems
#SCADA
#Vulnerability Analysis