Description:
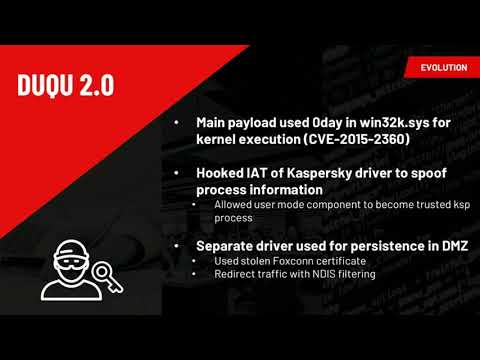
Explore kernel mode threats and practical defense strategies in this Black Hat conference talk. Delve into the evolution of OS security measures by Microsoft, including PatchGuard, Driver Signature Enforcement, and SecureBoot, and their impact on commodity kernel mode malware. Examine how advanced attackers bypass these protections and continue to leverage kernel mode malware. Learn about first-generation kernel threats, boot kits, and Secure Boot. Investigate Dooku Threats, Double Pulsar, and Hypervisor Code Integrity. Analyze implant design, including the Turla Driver Loader, and explore data-driven attacks, code reuse attacks, and kernel stack hooking. Discover techniques for hunting in the kernel, detecting threats like Double Pulsar, and implementing real-time detection. Evaluate the weaknesses and limitations of Windows platform security, and gain insights into improving your defensive tradecraft against kernel mode threats.
Kernel Mode Threats and Practical Defenses
Add to list