Description:
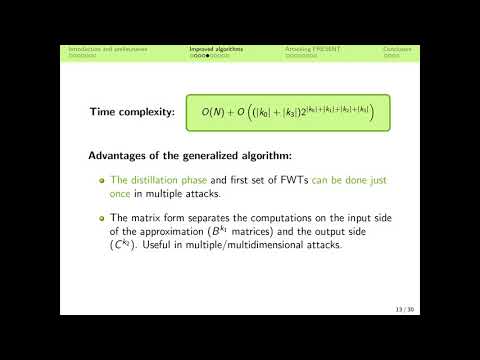
Explore a comprehensive analysis of improved key-recovery techniques in linear cryptanalysis, focusing on their application to the 28-round PRESENT block cipher. Delve into Matsui's Algorithm 2 for last-round attacks and examine the work of Collard et al. (2008) before discovering the main contribution: a generalized algorithm. Learn how to exploit key schedules, implement Walsh Transform pruning, and utilize the affine Pruned Walsh Transform. Investigate methods for combining correlations in multiple attacks and study linear approximations and distinguishers specific to PRESENT. Conclude with a detailed example of key recovery on 28-round PRESENT-80, compare various linear attacks on PRESENT, and explore open problems in the field.
Improving Key-Recovery in Linear Attacks - Application to 28-Round PRESENT
Add to list