Description:
Explore the process of reverse engineering and exploiting the macOS Zoom client in this HITB Security Conference talk. Delve into the journey of discovering a critical zero-interaction remote code execution vulnerability during a bug bounty event. Learn about the techniques and tools used for reverse engineering Objective-C apps, and gain insights into common exploitation methods applicable to various macOS applications. Understand the potential large-scale remote exploitation via the web and the implications for security. Discover the presenters' approach to the bounty, their logic in uncovering the flaw, and the steps taken to set up a download server and manipulate packages. Gain valuable knowledge on key takeaways, bug fixes, and the importance of collaboration in security research. Acquire practical skills in reverse engineering and exploiting macOS applications that can be applied beyond Zoom.
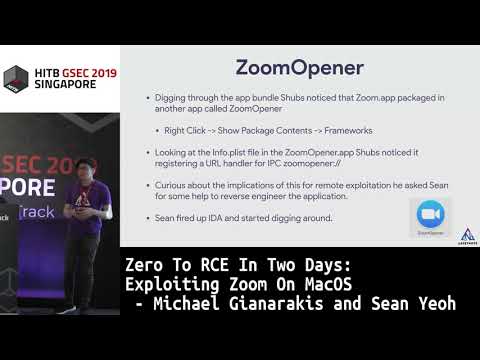
Exploiting Zoom on MacOS
Add to list
#Conference Talks
#Hack In The Box Security Conference
#Information Security (InfoSec)
#Cybersecurity
#Programming
#Programming Languages
#Objective C
#Reverse Engineering
#Personal Development
#Self Improvement
#Digital Skills
#macOS
#macOS Security