Description:
Explore the intricacies of electronic voting systems and second factor authentication in this comprehensive conference talk from the Hack In The Box Security Conference. Delve into the challenges of balancing privacy, integrity, security, and usability in electronic voting. Examine the concept of verifiability against untrusted devices and the importance of cast-as-intended verifiability. Learn about proof of correctness and the potential vulnerabilities in second factor authentication. Discover a novel approach to improving security through the introduction of a second factor correctness protocol. Analyze the roles of various actors in this system, including corrupted devices and validation devices. Gain insights into the QR code generation process, device protocols, and confirmation mechanisms. Conclude with a discussion on future work and potential improvements in electronic voting security.
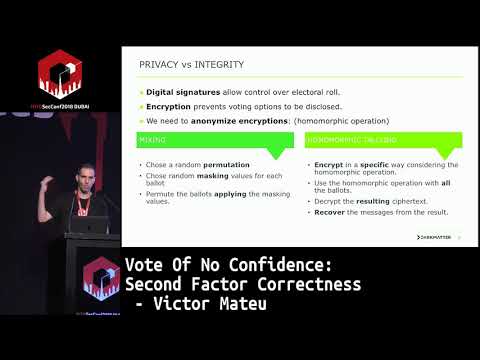
Vote of No Confidence - Second Factor Correctness
Add to list
#Conference Talks
#Hack In The Box Security Conference
#Social Sciences
#Political Science
#Electronic Voting
#Information Security (InfoSec)
#Cybersecurity
#Privacy