Description:
Explore how the European Union's General Data Protection Regulation (GDPR) can be exploited by social engineers to steal sensitive information in this 22-minute Black Hat conference talk. Delve into the "Right of Access" provision and its potential for abuse. Examine the challenges organizations face in verifying identity claims and the risks of making hasty decisions under time pressure. Learn about the flexible language in GDPR that can be manipulated, and understand the three problematic options available to businesses when handling data requests. Gain insights into proposed legislative solutions and best practices for data hygiene to mitigate these risks. Discover the implications for online businesses and legislators in addressing this critical security vulnerability in privacy laws.
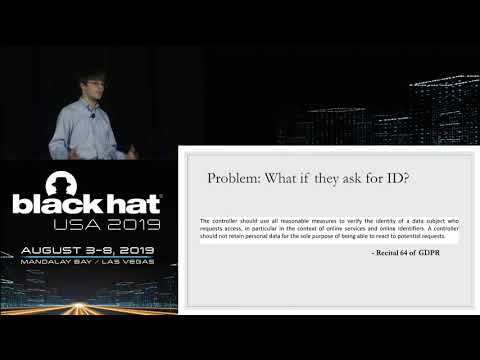
GDPRrrrr - Using Privacy Laws to Steal Identities
Add to list
#Conference Talks
#Black Hat
#Information Security (InfoSec)
#Cybersecurity
#Ethical Hacking
#Social Engineering
#Social Sciences
#Law
#Privacy Laws
#Identity Theft