Description:
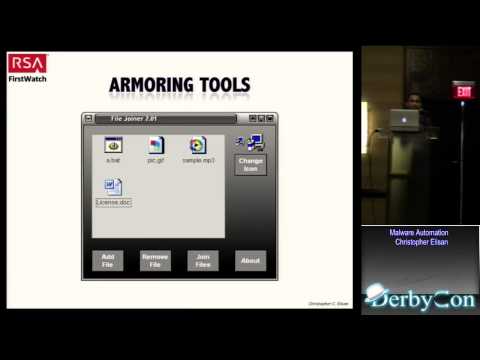
Explore malware automation techniques in this 48-minute conference talk from DerbyCon 3.0. Delve into the current state of malware development, from lone wolf operations to armies of armored malware. Learn about DIY kits, armoring tools, and AV scanners used in the process. Discover the advantages of malware automation, including its exponential effect and ease of updates. Gain insights into how cybercriminals attempt to bypass antivirus software and the implications for cybersecurity professionals.
Malware Automation
Add to list