Description:
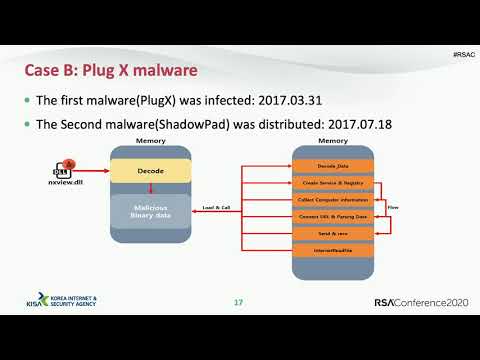
Explore a comprehensive analysis of supply chain attacks, focusing on the ASUS incident and various cases targeting Korean companies. Delve into two key strategies employed in these attacks: software development environment penetration and update server penetration. Examine artifacts, malware code similarities, and specific techniques used by attackers, including certificate signing, PlugX malware deployment, and selective infection methods. Learn about code tampering, DGA algorithms, and methods for hiding attacker IPs. Gain insights into the attackers' strategies mapped to the ATT&CK Matrix and discover practical applications of this knowledge in cybersecurity.
Chronicle of the Supply Chain Attack and Two Attack Strategies
Add to list
#Conference Talks
#RSA Conference
#Information Security (InfoSec)
#Cybersecurity
#Network Security
#Malware Analysis
#Incident Response
#Supply Chain Attacks