Description:
Explore techniques for hunting third-level domains in bug bounty programs during this informative video stream. Learn to utilize tools like sublist3r, eyewitness, and nmap while developing custom regex for automation. Gain insights into practical ethical hacking methods and enhance your skills in identifying potential vulnerabilities across subdomains. Discover strategies for effective bug bounty hunting and expand your knowledge of cybersecurity practices.
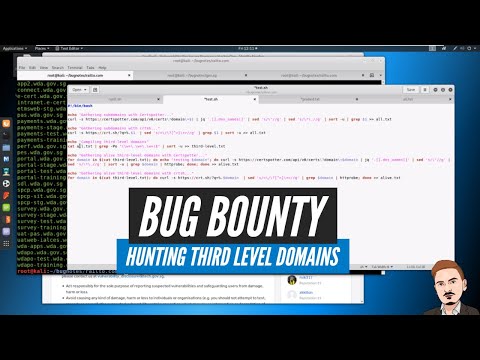
Bug Bounty - Hunting Third Level Domains
Add to list
#Information Security (InfoSec)
#Ethical Hacking
#Bug Bounty
#Cybersecurity
#Programming
#Domain-Specific Languages (DSL)
#Regular Expressions
#Network Security
#Nmap
#Subdomain Enumeration