Description:
Explore the concept of Bloom Filters in adversarial settings through this 22-minute conference talk. Delve into the applications, revisit the definition, and discover the Adversarial Resilient Bloom Filter. Learn about key contributions, including transformation techniques and the necessity of cryptographic functions. Examine proofs for the necessity of one-way functions and unsteady representations. Gain insights into unbounded adversaries and implementation strategies for robust Bloom Filters in challenging environments.
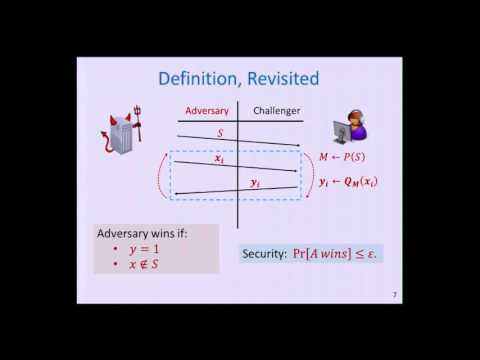
Bloom Filters in Adversarial Environments
Add to list
#Conference Talks
#Information Security (InfoSec)
#Cybersecurity
#Computer Science
#Cryptography
#Data Structures
#Bloom Filters