Description:
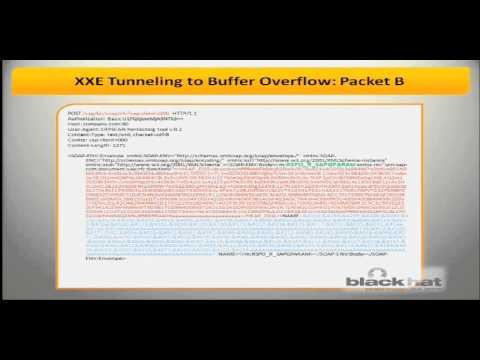
Explore a comprehensive analysis of Server Side Request Forgery (SSRF) attacks and their impact on business-critical applications in this Black Hat USA 2012 conference talk. Delve into the intricacies of SSRF vulnerabilities, with a focus on XXE Tunneling, and learn how these techniques can bypass multiple layers of security defenses. Discover how attackers can exploit trusted sources to compromise secured systems, using SAP as a practical example. Examine various SSRF vulnerabilities that enable internal network port scanning, unauthorized HTTP requests, and backend bruteforcing. Gain insights into the powerful XXE Tunneling technique and its potential to reopen old attack vectors and create new ones in business-critical systems. Learn about the OWASP-EAS project's XXEScanner tool, designed to gather critical information, perform scans, and execute attacks on vulnerable hosts or backends. Understand the implications of these attacks on enterprise resource planning (ERP) systems, portals, business intelligence platforms, and industrial control systems.
Read more
SSRF vs Business Critical Applications
Add to list
#Conference Talks
#Black Hat
#Information Security (InfoSec)
#Cybersecurity
#Penetration Testing
#Ethical Hacking
#Server-Side Request Forgery (SSRF)
#Security Vulnerabilities