Description:
Explore cutting-edge techniques in password hash reversal in this 59-minute conference talk from Bloomcon 2017. Delve into the intricacies of cryptographic hashes, password management policies, and the implications of the Ashley Madison leak. Learn about brute-forcing methods, rainbow tables, and their limitations. Discover innovative approaches like region tracking and Bloom filters for more efficient password cracking. Gain insights into space-time tradeoffs, data structures, and the latest developments in hash function analysis. Understand the potential impact of these advancements on cybersecurity and password protection strategies.
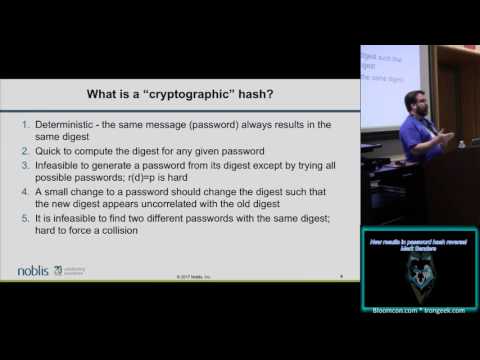
New Results in Password Hash Reversal
Add to list
#Conference Talks
#Information Security (InfoSec)
#Cybersecurity
#Computer Science
#Cryptography
#Data Structures
#Bloom Filters