Description:
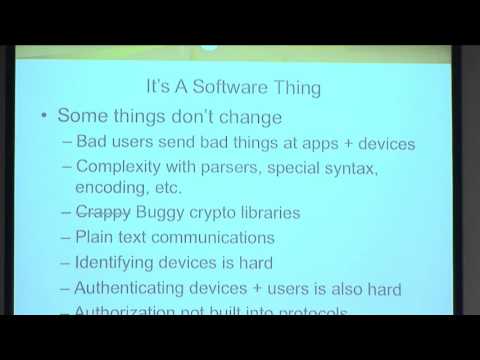
Explore the security landscape of IoT protocols in this 36-minute conference talk from LASCON 2015. Delve into the world of Machine-to-Machine (M2M) communications, focusing on MQTT and CoAP protocols designed for constrained devices. Understand why these protocols were developed as alternatives to HTTP for IoT applications. Examine their functionality, associated protocols, and common architectures. Witness demonstrations of potential attacks against these protocols and specific implementations, including device impersonation, system disruption, and remote code execution. Learn mitigation strategies for securing your own code and identify potential vulnerabilities in libraries and frameworks. Gain insights into pseudorandom number generation, DTLS, resource directories, publish-subscribe models, authentication, authorization, and Quality of Service (QoS) in IoT contexts. Enhance your understanding of IoT protocol security to develop more robust and secure real-world systems.
MQTT and CoAP - A Story about IoT Protocol Security
Add to list
#Conference Talks
#LASCON
#Information Security (InfoSec)
#Cybersecurity
#Computer Science
#Internet of Things
#MQTT
#Cryptography
#Encryption
#Authorization
#CoAP