Description:
Dive into a comprehensive 50-minute conference talk from Bloomcon 2017 exploring the intricacies of a Point of Sale (POS) breach investigation. Learn about POS malware, RAM scraping techniques, and the structure of both enterprise and SMB retail networks. Discover essential information gathering methods, develop an effective investigation plan, and analyze program execution, services, and registry entries. Explore lateral movement detection through security event logs, account escalation indicators, and the significance of OBJECTS.DAT files. Gain insights into card obfuscation challenges, process creation analysis, timeline construction, and the examination of remote access logs. Enhance your cybersecurity skills with this in-depth presentation on investigating POS security breaches.
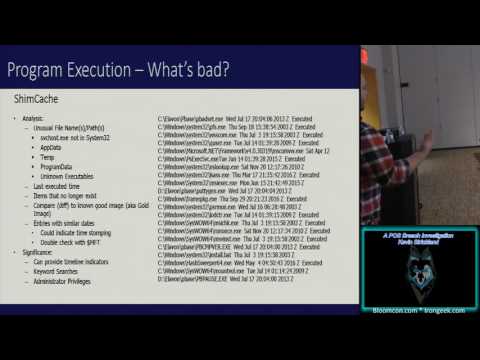
A POS Breach Investigation
Add to list
#Conference Talks
#Information Security (InfoSec)
#Cybersecurity
#Digital Forensics
#Personal Development
#Self Improvement
#Research Skills
#Information Gathering