Description:
Explore the security implications of the Rowhammer bug in DRAM cells through this 16-minute IEEE conference talk. Delve into how an unprivileged adversary can exploit this reliability issue to read bits in memory without directly accessing them, challenging the assumption that bit flips in private memory are harmless. Learn about novel techniques for exploiting the data dependence between Rowhammer-induced bit flips and nearby bits, enabling the deduction of sensitive information across security boundaries. Discover how this attack method threatens both integrity and confidentiality, even in systems with ECC memory. Examine an end-to-end attack on OpenSSH 7.9, extracting an RSA-2048 key from a root-level SSH daemon, and understand the innovative approaches used to manipulate memory and locate physically contiguous areas for double-sided Rowhammering. Gain insights into the broader implications of this research for DRAM security and the need for robust countermeasures against such sophisticated attacks.
Read more
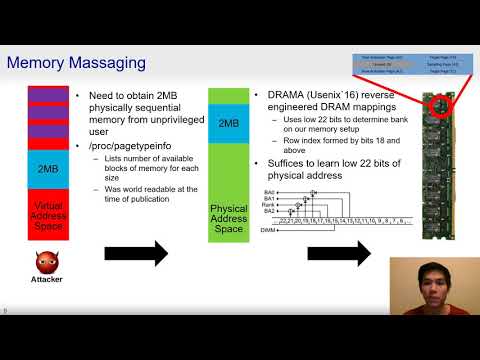
RAMBleed - Reading Bits in Memory Without Accessing Them
Add to list
0:00 / 0:00