Description:
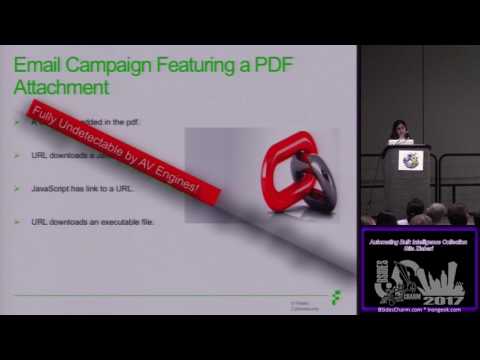
Learn to automate bulk intelligence collection for cybersecurity analysis in this BSidesCharm 2017 conference talk. Explore when and what to automate in data mining processes, focusing on extracting valuable information from malware files, emails, and various document types. Discover techniques for finding critical data in large datasets, preparing result checklists, and considering database integration. Follow along as the speaker demonstrates manual analysis methods, extracts malicious domains from different file formats, and analyzes email campaigns with suspicious attachments. Gain insights into using known tools for analysis, including Foremost for file extraction. Get introduced to the Yalda framework for data storage and quality control in automated intelligence gathering. Access the code on the Fidelis GitHub repository to implement these automation techniques in your own cybersecurity workflows.
Automating Bulk Intelligence Collection
Add to list
#Conference Talks
#Data Science
#Data Mining
#Information Security (InfoSec)
#Cybersecurity
#Malware Analysis
#Computer Science
#Database Management
#Data Storage
#Engineering
#Manufacturing
#Quality Control
0:00 / 0:00